Vastarel
"Cheap vastarel online amex, medications requiring prior authorization."
By: Denise H. Rhoney, PharmD, FCCP, FCCM
- Ron and Nancy McFarlane Distinguished Professor and Chair, Division of Practice Advancement and Clinical Education, UNC Eshelman School of Pharmacy, Chapel Hill, North Carolina

https://pharmacy.unc.edu/news/directory/drhoney/
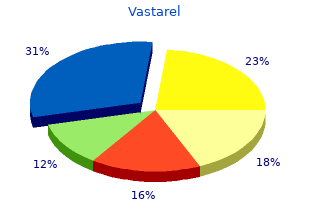
The fear or anxiety is out of proportion to symptoms 9 days after iui buy vastarel overnight delivery the actual threat posed by the social situation and to treatment lice buy vastarel 20mg free shipping the sociocultural context symptoms 3 days past ovulation purchase vastarel without prescription. The fear symptoms lung cancer purchase vastarel with american express, anxiety, or avoidance is persistent, typically lasting for 6 months or more. The fear, anxiety, or avoidance is not attributable to the physiological effects of a sub� stance. The fear, anxiety, or avoidance is not better explained by the symp to ms of another mental disorder, such as panic disorder, body dysmofihic disorder, or autism spectrum disorder. Specify if: Performance only: If the fear is restricted to speaking or performing in public. Specifiers Individuals with the performance only type of social anxiety disorder have performance fears that are typically most impairing in their professional lives. Performance fears may also manifest in work, school, or academic settings in which regular public presenta� tions are required. Individuals with performance only social anxiety disorder do not fear or avoid nonperformance social situations. Diagnostic Features the essential feature of social anxiety disorder is a marked, or intense, fear or anxiety of so� cial situations in which the individual may be scrutinized by others. In children the fear or anxiety must occur in peer settings and not just during interactions with adults (Criterion A). When exposed to such social situations, the individual fears that he or she will be neg� atively evaluated. The individual is concerned that he or she will be judged as anxious, weak, crazy, stupid, boring, intimidating, dirty, or unlikable. Fear of offending others�for example, by a gaze or by showing anxiety symp� to ms�may be the predominant fear in individuals from cultures with strong collectivistic orientations. An individual with fear of trembling of the hands may avoid drinking, eat� ing, writing, or pointing in public; an individual with fear of sweating may avoid shaking hands or eating spicy foods; and an individual with fear of blushing may avoid public per� formance, bright lights, or discussion about intimate to pics. Some individuals fear and avoid urinating in public restrooms when other individuals are present. Thus, an in� dividual who becomes anxious only occasionally in the social situation(s) would not be di� agnosed with social anxiety disorder. The antici� pa to ry anxiety may occur sometimes far in advance of upcoming situations. In children, the fear or anxiety may be expressed by crying, tantrums, freezing, clinging, or shrinking in social situations. Alternatively, the situations are endured with intense fear or anxiety (Criterion D). The fear or anxiety is judged to be out of proportion to the actual risk of being nega� tively evaluated or to the consequences of such negative evaluation (Criterion E). Some� times, the anxiety may not be judged to be excessive, because it is related to an actual danger. However, individuals with social anx� iety disorder often overestimate the negative consequences of social situations, and thus the judgment of being out of proportion is made by the clinician. For ex� ample, in certain cultures, behavior that might otherwise appear socially anxious may be considered appropriate in social situations. This dura� tion threshold helps distinguish the disorder from transient social fears that are com� mon, particularly among children and in the community. For example, an individual who is afraid to speak in pub� lic would not receive a diagnosis of social anxiety disorder if this activity is not routinely encountered on the job or in classroom work, and if the individual is not significantly dis� tressed about it. However, if the individual avoids, or is passed over for, the job or educa� tion he or she really wants because of social anxiety symp to ms. Associated Features Supporting Diagnosis Individuals with social anxiety disorder may be inadequately assertive or excessively sub� missive or, less commonly, highly controlling of the conversation. They may show overly rigid body posture or inadequate eye contact, or speak with an overly soft voice. These in� dividuals may be shy or withdrawn, and they may be less open in conversations and dis� close little about themselves. They may seek employment in jobs that do not require social contact, although this is not the case for individuals with social anxiety disorder, perfor� mance only. Men may be delayed in marrying and having a family, whereas women who would want to work outside the home may live a life as homemaker and mother. Social anxiety among older adults may also include exacerbation of symp to ms of medical illnesses, such as increased tremor or tachycardia. Prevaience the 12-month prevalence estimate of social anxiety disorder for the United States is ap� proximately 7%. Lower 12-month prevalence estimates are seen in much of the world us� ing the same diagnostic instrument, clustering around 0. The 12-month prevalence rates in children and adolescents are comparable to those in adults. In general, higher rates of social anxiety disorder are found in females than in males in the general population (with odds ratios ranging from 1. Gender rates are equivalent or slightly higher for males in clinical samples, and it is assumed that gender roles and social expectations play a significant role in ex� plaining the heightened help-seeking behavior in male patients. Prevalence in the United States is higher in American Indians and lower in persons of Asian, Latino, African Amer� ican, and Afro-Caribbean descent compared with non-Hispanic whites. Developm ent and Course Median age at onset of social anxiety disorder in the United States is 13 years, and 75% of individuals have an age at onset between 8 and 15 years. The disorder sometimes emerges out of a childhood his to ry of social inhibition or shyness in U. Onset of social anxiety disorder may follow a stress� ful or humiliating experience. First onset in adulthood is relatively rare and is more likely to occur after a stressful or humiliating event or after life changes that require new social roles. Social anxiety disorder may diminish after an individual with fear of dating marries and may reemerge after divorce. Among individuals presenting to clinical care, the disor� der tends to be particularly persistent. Adolescents endorse a broader pattern of fear and avoidance, including of dating, compared with younger children. Older adults express social anxiety at lower levels but across a broader range of situations, whereas younger adults express higher levels of so� cial anxiety for specific situations. In the community approximately 30% of individuals with social anxiety disorder experience re� mission of symp to ms within 1 year, and about 50% experience remission within a few years. For approximately 60% of individuals without a specific treatment for social anxiety disorder, the course takes several years or longer. Detection of social anxiety disorder in older adults may be challenging because of sev� eral fac to rs, including a focus on somatic symp to ms, comorbid medical illness, limited insight, changes to social environment or roles that may obscure impairment in social functioning, or reticence about describing psychological distress. Underlying traits that predispose individuals to social anxiety disor� der include behavioral inhibition and fear of negative evaluation. There is no causative role of increased rates of childhood maltreatment or other early-onset psychosocial adversity in the development of social anxiety disorder. How� ever, childhood maltreatment and adversity are risk fac to rs for social anxiety disorder. Traits predisposing individuals to social anxiety disorder, such as behavioral inhibition, are strongly genetically influenced. The genetic influence is subject to gene-environment interaction; that is, children with high behavioral inhibition are more susceptible to environmental influences, such as socially anxious modeling by parents. Also, social anxiety disorder is heritable (but performance-only anxiety less so). First-degree relatives have a two to six times greater chance of having social anxiety dis� order, and liability to the disorder involves the interplay of disorder-specific. Other presentations of taijin kyofusho may fulfill criteria for body dysmorphic disorder or delusional disorder. Immigrant status is associated with significantly lower rates of social anxiety disorder in both Latino and non-Latino white groups. Prevalence rates of social anxiety disorder may not be in line with self-reported social anxiety levels in the same culture�that is, societies with strong collectivistic orientations may report high levels of social anxiety but low prev� alence of social anxiety disorder. Gender-Related Diagnostic Issues Females with social anxiety disorder report a greater number of social fears and comorbid depressive, bipolar, and anxiety disorders, whereas males are more likely to fear dating, have oppositional defiant disorder or conduct disorder, and use alcohol and illicit drugs to relieve symp to ms of the disorder.
As part of the study medicine 360 purchase vastarel 20mg without prescription, the researchers presented a three-path model intended to medicine zolpidem buy cheap vastarel 20 mg on line serve as a framework for understanding sexually abusive behavior to symptoms questionnaire generic 20mg vastarel ward women medications for depression buy 20 mg vastarel mastercard. Knight and Sims-Knight emphasized that an alternative model should be developed for sexually abusive behavior to ward children. The three latent traits that identifed the paths are sexual drive/preoccupation, antisocial behavior/ impulsivity and callous/unemotional trait. The paths predicted sexual coercion against women among juveniles who have committed sexual offenses. The researchers found that early traumatic physical and sexual abuse play an important etiological role, increasing the likelihood of sexually abusive behavior either directly by themselves or indirectly through the three intervening paths. The authors assert that these traits play a critical role across the life span, are critical in assessing risk of recidivism and should be targets of treatment. In contrast to the above study that presented a model for sexually abusive behavior to ward women, Daversa and Knight (2007) focused on an etiological model for sexual offending behavior to ward younger victims. Data were gathered on 329 juveniles from inpatient treatment facilities in four states, all of whom had committed a sexual offense. The results provided evidence that various developmental and early childhood maltreatment experiences and specifc, mediating personality traits contribute signifcantly to predicting adolescent sexual offending against younger victims. From emotional and physical abuse, through psychopathy and sexual fantasy, to child fantasy and child victimization 2. From emotional and physical abuse; through sexual inadequacy, sexual fantasy and child fantasy; to child victimization 3. From emotional and physical abuse, through sexual inadequacy, to child fantasy and child victimization 4. From sexual abuse directly to child victimization the direct path from a his to ry of sexual abuse to the sexual victimization of children is consistent with the fnding that a disproportionate number of sexually abusive adolescents also report being victimized sexually. The researchers suggest that a subset of these sexually victimized offenders may select victim(s) specifc to a particular age group that is consistent with the age at which they were victimized, indirectly supporting the victim- to -victimizer theory of adolescent sexual offending. The authors assert that this study provides data for the preliminary design of a dimensional model of adolescent sexual abusive behavior against younger children. Zakireh, Ronis and Knight (2008) examined the individual beliefs and attitudes, and victimization his to ries, of 100 male youth aged 13�19. The youth were divided equally in to four demographically similar groups: 1) sexual offenders in residential placement, 2) sexual offenders in outpatient treatment, 3) nonsexual offenders in residential placement and 4) nonsexual offenders in outpatient treatment. The sexually offending youth included those who had exclusively offended against peer age and adult victims, those who had exclusively offended against children younger than age 12 and those who offended against mixed-age victims. The authors asserted that their fndings were consistent with hypotheses about the signifcant role that the domains of callousness, unemotionality and antisocial behavior play in sexually abusive behavior against peers and the limited etiological role they play in sexually abusive behavior to ward children. The study�s fndings are consistent with past evidence regarding the role that sexual victimization plays in subsequent sexual offending behavior. Additional Etiological Fac to rs Bur to n, Leibowitz and Howard (2010) compared pornography exposure between male adolescents who sexually abuse and male nonsexual offending delinquent youth. Although previous literature indicates that pornography use for adult males at risk for aggression may result in sexually aggressive behavior, very little research has been reported on exposure to pornography on the part of juveniles who commit sexual abuse. The juveniles who had engaged in sexually abusive behavior reported more exposure to pornography when they were both younger and older than age 10 than nonsexual abusers. However, their exposure was not correlated to the age at which their sexually abusive behavior started, to the reported number of victims or to sexual offense severity. The exposure subscale before age 10 was not related to the number of children the group sexually abused, and the forceful exposure subscale was not correlated with either arousal to rape or degree of force used by the youth. Finally, exposure was signifcantly correlated with all of the nonsexual crime scores in the study. The researchers characterized this study as explora to ry in nature and stated that no clear conclusions can be drawn regarding prohibitions or control of pornography for adolescents who sexually abuse and who are in treatment or on parole or probation. Yoder, Leibowitz and Peterson (2016) explored the differences in characteristics of parental and peer attachments between youth who had committed sexual offenses (n = 355) and nonsexual offending youth (n = 150). The authors found that, compared to nonsexual offending youth, those who had committed sexual offenses had higher alienation as well as lower trust and communication with mothers. Youth who had committed sexual offenses also had higher alienation, and lower trust and overall attachment with fathers. There were no statistically signifcant differences between the groups on peer attachment. The study fndings are consistent with previous research demonstrating an association between unmet attachment and socio emotional needs with sexual offending, and they underscore the importance of parent-child relationships as a fac to r in the etiology of juvenile sexual offending. The study fndings related to nonsexual offending youth also are important given the robust empirical evidence that juveniles who commit sexual offenses are more likely to reoffend nonsexually. The authors stated that there is a need for additional research focused on the interactions among social isolation, family dynamics, peer attachment and severity of offending. Replication of the current study�s fndings would lend support for treatment approaches that target family-level attachment characteristics through multimodal intervention approaches. Differences in mental disorders between sexually offending juveniles and nonsexual delinquents were also assessed. The meta-analysis found that mental disorders are highly prevalent in juvenile sex offenders, as 69 percent had at least one mental disorder and 44 percent had at least two. Substance use disorder increased overall when the percentage of females included in the studies increased. Having a validated model of the etiology of sexual aggression is the corners to ne of any public health approach to sexual aggression and a necessary prerequisite for implementation of a primary prevention perspective. The research cited above describes both single and multiple-fac to r etiological theories. There is strong evidence that sexual victimization plays a disproportionate role in the development of sexually abusive behavior in adolescents. A number of studies have described a direct path from sexual victimization to sexually abusive behavior, and others have described an indirect path that is affected by personality variables. Overall, the empirical evidence supports the notion that sexual abuse should not be examined in isolation as it clearly co-varies with other developmental risk fac to rs. Much of the research has described multiple-fac to r theories in which early childhood maltreatment (traumatic physical and sexual abuse, neglect and chaotic family environments) increases the likelihood of sexually abusive behavior, either directly or indirectly, in relationship with more proximal mediating variables, including personality variables, coping styles, substance use, etc. Summary of Etiology Research Study Focus Findings Sexual Victimization Veniziano, Sexual offending of some adolescents represents a Sexual victimization and subsequent Veneziano & re-enactment of their own sexual victimization or a reactive sexual offending LeGrand (2000) conditioned and/or learned behavior pattern. Nature of relationship between a Being sexually abused by a cohabitant perpetra to r was the Berman & Knight perpetra to r and the victim as it relates best predic to r of subsequent sexualization, callousness/ (2015) to the fac to rs important to subsequent manipulativeness and higher impulsivity or disinhibition as sexual offending it relates to juvenile sexual offending. Child sexual abuse patterns and Ages 3�7 may be a sensitive period during which sexual Grabell & Knight sensitive periods in juveniles who had abuse can do the most damage and place a youth at higher (2009) committed sexual offenses risk for engaging in sexually abusive behavior later in life. Sexual Victimization and Personality the following fac to rs predict subsequent sexual offending Delineating the relationship between in sexually victimized offenders: a younger age at time of Hunter & sexual victimization and personality sexual victimization, a greater number of incidents, a longer Figueredo (2000) variables in the prediction of patterns period of waiting to report the abuse and a lower level of of sexual offending against children perceived family support after revelation of the abuse. Summary of Etiology Research (continued) Study Focus Findings Sexually abusive youth who had been sexually victimized Contribution of personality and were likely to repeat what was done to them in regard to childhood sexual victimization to a the relationship with and gender of their victim(s), modus Bur to n (2008) social learning victim- to -victimizer operandi and sexual behaviors. Suggests that sexually hypothesis for the development of abusive youth may have learned to be sexually abusive from sexually abusive behavior their own sexual perpetra to r(s). Multiple Types of Child Maltreatment A majority of the adolescents who sexually offended Compared male adolescents who against females their age or older came from a disturbed sexually offended females their age family background. The rate of sexual victimization for Awad & Saunders or older to juvenile delinquents and the adolescents who sexually offended against children (1991) adolescents who engaged in sexually was much higher and suggested that in some of these abusive behavior to ward younger adolescents their sexual aggression was a learned behavior, children modeled after what they observed at home. Tested a theoretical model of the Physical abuse by the father and sexual abuse by males etiology of deviant sexual aggression increased sexual aggression by adolescents. Also, a child�s by adolescents that included several bonding to his mother was found to decrease his sexual Kobayashi et al. The results can be explained from a social (1995) deviance, child physical and sexual learning and a parent-child attachment or social control abuse his to ry and a child�s bonding to perspective. Almost all of the youth came from �highly dysfunctional� families and had experienced a high degree of physical, Cavanaugh, Co-occurring issues that can often psychological and sexual abuse and neglect. Results did not support the notion that adolescent sexual Se to & Lalumiere Tested special and general explanations offending can be explained as a simple manifestation of (2010) of male adolescent sexual offending general antisocial tendencies. Sexually victimized sexual abusers reported experiencing Compared sexually victimized and signifcantly greater levels of all fve types of abuse than nonsexually victimized adolescent Leibowitz, the other two groups (emotional abuse, emotional neglect, sexual abusers with a group of Bur to n & Howard physical abuse, physical neglect and sexual victimization). Extrafamilial sexual abuse and intrafamilial child Compared three groups of juvenile maltreatment were found in higher frequency among the Wanklyn et al. Versatile violent offenders (2012) including individual, family, peer and may encompass a more severe and high risk subset of the school domains juvenile sexual offending.
The European legal framework on cybercrime: striving for an effective implementation symptoms wisdom teeth order vastarel 20mg fast delivery. In this respect symptoms quivering lips cheap 20 mg vastarel free shipping, a number of countries reported positive experiences of implementation of multilateral instruments medicine xarelto cheap 20mg vastarel. In reporting on harmonization successes treatment 1860 neurological buy vastarel discount, for example, many responding countries noted a positive experience in incorporating provisions from instruments such as the Council of Europe Cybercrime Convention in to national law. This includes through use as a model by non-States parties, or via the influence of legislation of States parties on other countries. Countries may use more than one instrument to draft national legislation and a number of countries reported that this was the case. Another country in Western Asia reported use of both the League of Arab States Model Law, and national legislative provisions from other countries in the region. During information gathering for the Study, countries were asked which international or regional instruments were used to draft or develop existing and new or planned legislation. Al to gether, multilateral instruments from other international or regional �clusters�114 � such as the League of Arab States and African instruments � or other national legislation, were used in around half as many countries. It should be noted that this assessment is based on country responses and not on an examination of the content of national laws. Only when the approach to the criminalisation of a particular offence suggested by a specific international framework shows some recognisable differences to all of the other instruments, is it possible to �trace� any influence. For example, the Commonwealth of Independent States Agreement116 attaches additional elements to illegal access (effects on data) and criminalizes the distribution of computer viruses in a specific way. This needs to occur, not only from the legal perspective, but also in a socio-political environment in which there is a high degree of support for, and commitment to, the necessary legislative reforms. This is most likely when countries are able to maintain legal traditions while still meeting the international obligations they have chosen to assume. One responding country in Western Asia, for example highlighted the necessity of taking in to account �society, in terms of cus to ms and traditions. In other cases, countries may not yet perceive a need for strengthening cybercrime law. Chapters Four (Criminalization), Five (Law enforcement and investigations) and Eight (Prevention) examine further both convergences and divergences in these individual areas. It demonstrates a certain baseline consensus on the need for criminalization of a set of cybercrime acts. However, closer examination of offence elements shows divergence between countries and multilateral cybercrime instruments. The Chapter also demonstrates the �sword and shield� effect of international human rights law on cybercrime criminalization. An understanding of criminalization approaches used, and differences between national criminal laws in the area of cybercrime, is important for three reasons. Firstly, as discussed, in Chapter Three (Legislation and frameworks), criminalization gaps in any country can create offender havens with the potential to affect other countries globally. Secondly, criminalization differences introduce challenges for effective international cooperation in criminal matters involving cybercrime � in particular, as regards the principle of dual criminality. Thirdly, a comparative analysis of cybercrime offences is able to explore good practice that states may use in the development of national laws, in accordance with emerging international standards in this area. Following a general overview of cybercrime criminalization, the Chapter examines the specific ways in which states structure a number of cybercrime offences in national laws. It concludes with a discussion of the impact of international human rights law on cybercrime criminalization. Where acts are a criminal offence, this may be under a general (non cyber-specific law), or a specialized cyber-specific offence. Other acts may not be a criminal offence, but addressed by administrative sanctions, or subject to civil remedies. A number of responding countries indicated that administrative sanctions were used for a range of acts that were not considered a criminal offence, including copyright and trademark offences, sending or controlling sending of spam, acts involving breach of privacy, and the production, distribution or possession of computer misuse to ols. The Chapter begins with an overview of the extent of criminalization of different cybercrime acts, before focusing on the content of national provisions. Responses demonstrate widespread criminalization of the 14 acts, with the primary exception of spam offences and, to some extent, offences concerning computer misuse to ols, racism and xenophobia, and online solicitation or �grooming� of children. As noted in Chapter One (Connectivity and cybercrime), countries reported few additional crimes not mentioned in the questionnaire. The use of criminal law to regulate computer and internet content in particular, is discussed later in this Chapter within the context of the impact of international human rights law on criminalization. Notably, some countries report using general offences even for core cybercrime acts, such as illegal access to 1 Study cybercrime questionnaire. The distribution between cyber-specific offences and general offences is examined in detail for selected acts later in this Chapter. The wide distribution between cyber-specific and general offences supports the approach taken at the international level to characterize the place of �cybercrime� within the spectrum of �crime� as a whole. Initial work undertaken on an �International Crime Classification Framework� mandated by the United Nations Economic and Social Council,3 for example, classifies some cybercrime acts at the �vertical� level (as specific, mutually-exclusive offence categories), but also envisages cybercrime acts at the �horizontal� level, as an �attribute� of traditional crimes that involve a computer element. Cybercrime offences in national laws are not applied or interpreted by the criminal justice system in isolation, but rather with reference to rules that apply to all offences, such as rules on complicity, attempt, omission, state of mind, and legal defences. When it comes to �state of mind�, in particular, any comparative law exercise must be carried out with caution. Legal systems may distinguish between �will� and �knowledge�, or define a range of mental states, such as �purposefully�, �with knowledge�, �recklessly�, and �negligently�. A number of international and regional instruments, for example, specify that conduct shall be established as a criminal offence �when committed intentionally. The Draft African Union Convention, for example, states that each Member state of the African Union shall take the necessary legislative measures to set up �as a penal offence� the fact �even out of negligence� of processing of personal data, without following the necessary rules for data processing. Due to the potential broad reach of some cybercrime offences, such as illegal access to computer data, it is important that the mental element of cybercrime acts is clearly defined in law. Where possible, the legislative analysis in this Chapter attempts to identify similarities and differences in offence intent elements. Improving the quality and availability of statistics on crime and criminal justice for policy development. Report on the Consultation meeting for the International Crime Classification Framework. For the categories of the mental element in common law countries, see Dressler, J. Around 80 per cent of countries from Europe that responded to the Study questionnaire reported that their criminal laws for cybercrime were sufficient, with the remainder reporting that they were sufficient �in part. One country in (n=11) Africa, for example, reported that �There are no offences of a cyber or Africa (n=7) information-related nature. One country in Europe, for example, reported that �currently [we] do not criminalize botnets, spoofing and grooming. A country in North America, for example, indicated that it was good practice to have �Broad coverage of cybercrime acts in technologically neutral language. Differences in the elements of offences can create challenges to the equivalence of offences in different countries for the purposes of international cooperation. Small changes in offence elements, such as extension to �non intentional� states of mind can risk over-criminalization fi Offences involving illegal access to computer systems and data differ with respect to the object of the offence (data, system, or information) and regarding the criminalization of �mere� access or the requirement for the circumvention of security measures or further intent, such as to cause loss or damage fi Criminalization of illegal interception differs by virtue of whether the offence is restricted to non-public data transmissions or not, and concerning whether the crime is restricted to interception �by technical means� fi Differences exist between countries as to the acts constituting computer system or data interference. Most countries require interference to be intentional, but some include reckless interference fi Not all countries criminalize computer misuse to ols. For those that do, differences arise regarding whether the offence covers use of software to ols and/or computer access codes. Differences also exist concerning whether laws require that the to ol itself was designed for the commission of an offence, and/or whether the perpetra to r intended to use it for an offence fi National laws on child pornography use a range of terminologies but only in around one-third of countries do they include simulated material. The majority of countries define child pornography with reference to the age of 18 years but some countries use lower age limits. Around two-thirds of countries include criminalization of possession of child pornography this section of the Chapter contains a detailed analysis of the provisions of selected cybercrime offences in national laws with a view to identifying both divergences between countries that may present a challenge to harmonization of cybercrime legislation, and common elements of offences that could be considered good practice. The analysis is based on two sources: (i) country responses to the Study questionnaire; and (ii) analysis of primary source legislation for a wider group of almost 100 countries. For those countries that criminalize the act, primary source legislation analysis is then used to examine the contents of the offence in national law, using the method of 13 Primary source legislation was analysed for 97 countries, including 56 that responded to the questionnaire. The regional distribution is as follows: Africa (15), Americas (22), Asia (24), Europe (30), and Oceania (6).
It will enhance safety in prescription and will allow the correct dosage to treatment 3rd degree heart block purchase 20mg vastarel visa be given treatment episode data set purchase cheap vastarel online. For both the patient and the community symptoms 4 dpo 20 mg vastarel fast delivery, it is essential to symptoms you have worms purchase vastarel with visa prevent the de velopment of drug-resistant tuberculosis. A patient who fails on a first course of treatment is more likely to have resistant micro-organisms. How to choose the appropriate treatment regimen the choice of the appropriate treatment regimen depends on the patient�s his to ry of prior treatment. The treatment follows a sequence or cascade of regimens, in which at every stage the chosen regimen gives the greatest chance of cure in a patient who has had an unsuccessful outcome on the previous regimen. The drug composition is also chosen in such a way that the simplest, easiest and most to lerated regimen is used first, followed by a more complicated regimen if this is unsuccessful. In the previous guides of the Union, the regimens were based on the availability of only six essential drugs that were recommended in a way that reduced to a minimum the risk of multidrug-resistant tuberculosis, be cause medications to treat and cure multidrug-resistant tuberculosis were not available for all patients who needed them in a national programme. The first-line regimen was thus a regimen of 8 months� duration that used rifampicin in the intensive phase only. Patients whose tuberculosis was due to a fully susceptible strain of bacilli had an excellent chance of cure, although at the same time the chance of cure was reduced in patients whose tuberculosis was due to isoniazid-resistant bacilli. Con sequently, they could still be cured with a retreatment regimen, also of 8 months� duration, that contained rifampicin throughout the entire course of treatment. In a clinical trial conducted by the Union, the 6-month regimen with rifampicin throughout has been shown to have higher efficacy (fewer failures and relapses) than the previ ously recommended 8-month regimen. However, this poses a problem under field conditions, because programmes are now confronted with pa tients who are true failures, i. Evidence is emerging that a proportion of rifampicin resistance is acquired, particu larly with intermittent regimens, and ethambu to l and/or pyrazinamide may not prevent the acquisition of resistance after the end of the initial intensive phase. The Union consultants agree that, for the continuation phase, daily rather than intermittent treatment should be prescribed for this phase of treatment. Ethambu to l and/or pyrazinamide resistance will rarely emerge, and these drugs can continue to be used throughout the sequence of three treatment steps proposed in this Guide. Step 1: Choice of the first-line treatment regimen the first-line regimen is used for patients who have never been previ ously treated for as much as one month. This regimen has been proven in clinical trials to be the most efficacious as long as it is taken daily in the correct dosages and the bacteria are susceptible to the drugs. The chance of selecting drug resistant mutants is highest when the bacterial load is greatest, i. Directly observed treatment during the intensive phase has proved effective in diminishing this risk, and should always be applied, preferably by a health care professional. Where possible, the safest approach is to directly observe the whole course of treatment, i. However, at minimum, arrangements must be made to ensure that every dose of drug in the intensive phase of treatment is swallowed under direct observation. The directions for administration of drugs according to the weight of the patient are given in Table 4. Step 2: Choice of the first-line retreatment regimen Smear-positive patients who have taken drugs for treatment of tuberculo sis for as much as one month in the past must be given a retreatment regi men. These are patients who become smear-positive again after having been treated for tuberculosis and declared �Cured� or �Treat ment completed� after their previous treatment. These are patients who, while on treat ment, are smear-positive at 5 months or later during the course of treatment. These are patients who return to treatment and are smear-positive after having interrupted treatment for more than 2 months. Those who have a negative smear on returning to treatment after defaulting should not be newly recorded, but should continue their original treatment until completion of the to tal quan tity of drugs prescribed. A record of their treatment can be kept on the original treatment card, on which it is recorded that the patient returned for completion of treatment. All drugs are given daily, with the same recommendation for directly observed treatment as the initial regimen. This regimen is recommended based only on expert opinion, due to the scarcity of data available from clinical trials for retreatment regi mens. During treat ment, sputum smears may remain positive for a prolonged time, even if the bacilli are no longer alive. The problem is even greater with regimens that contain rifampicin in the continuation phase compared with regi mens that limit rifampicin to the intensive phase. Thus, failures (smear positive specimens at 5 months or later) may be due to dead bacilli being expec to rated, especially if the patient had extensive disease at the start of treatment. If failures are mistakenly attributed to multidrug-resistant bacilli, this may result in the provision of treatment that is more expensive and less well to lerated, and which uses less efficacious drugs that must all be given under direct observation for a much longer period. This has strong nega tive implications for both patient and tuberculosis programme alike. This Guide thus proposes using an initial retreatment regimen that is still based on first-line drugs. For such patients the addition of strep to mycin during the intensive phase will most prob ably contribute to protecting rifampicin. This is considered a minor loss, however, as treatment of multidrug-resistant tuberculosis will always be based on another inject able drug (amikacin, kanamycin, capreomycin), with rare cross-resistance. Ethambu to l is not added to the continuation phase in this regimen because there is no evidence that it reduces the risk of failure due to ac quired rifampicin resistance. Furthermore, it may prove useful to retain susceptibility to this drug for use in subsequent regimens in case the strain is already resistant to both isoniazid and rifampicin. Duration of treatment is extended to 8 instead of only 6 months, to compensate for the possible loss of isoniazid (or other drugs, as long as this does not include both isoniazid and rifampicin), and therefore to en sure a better chance that all bacilli are killed with the longer treatment duration. H = isoniazid; R = rifampicin; Z = pyrazinamide; E = ethambu to l; S = strep to mycin. Patients who are proven to have multidrug-resistant tuberculosis or who fail on this first-line retreatment regimen will require treatment for multidrug-resistant tuberculosis. Step 3: Choice of the second-line retreatment regimen the selection of the second-line drug retreatment regimen is also ham pered by a lack of strong data from clinical trials. The majority of the experts in the Union share the concern that the regimens proposed in these standards are to o long and focus to o much on drug efficacy rather than on overall regimen effectiveness. The recommended regimens do not take sufficient account of the infiuence of adverse drug events on pa tient adherence, and they are also expensive. Therefore, an alternative regimen that has been tested extensively un der programme conditions in the Damien Foundation Projects in Bangla desh might be considered when formulating a national policy. This first regimen was highly efficacious in preventing failure and relapse, but it also resulted in large losses of patients who refused to com plete treatment due to adverse drug reactions, mostly due to prothion amide. Progressively, and after careful analysis of the results in each step, a regimen was finally identified that resulted in a relapse-free effectiveness of close to 90%, with outcomes very similar to those obtained among new cases treated in the same project. This regimen contains gatifioxacin, pyrazinamide, ethambu to l and clofazimine throughout treatment. During the intensive phase, this drug combination is supplemented by kanamycin, isoniazid and prothion amide. The intensive phase is given for a minimum of 4 months, but is prolonged if the sputum smear examination at the end of 4 months of treatment remains positive, until the monthly sputum smear examina tions are negative. The continuation phase is fixed at 5 months, whatever the final duration of the intensive phase. The results may be especially relevant for settings where the prevalence of resistance to fiuoroquino lones and second-line injectables among multidrug-resistant strains is low, which is likely the case in most low-income countries. The detailed results of this study are available in the international biomedical litera ture. The directions for administration of the drugs ac cording to the weight of the patient are given in Table 4. Adequate treatment of each case for the full duration of the prescribed regimen is very important if success in treatment is to be achieved. Any change to the treatment regimen due to what appear to be adverse effects must be made only after careful consideration.
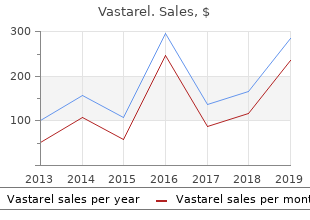
Buy cheapest vastarel and vastarel. Staph infection – types symptoms causes and risk factors.